For the last days, I was working to get my ISP connection @home (Which is from KPN) working with a FortiGate firewall. Well, it was a bit of a puzzle to get this working because information about this topic is very fragmented to find. So, I want to write about what I’ve done to get this working.
What do I have?
- Internet from KPN (dutch ISP) with FTTH (Fiber-to-the-home) 200/200 Mbps
- Interactive-TV from KPN
- I do not use telephony from KPN
- Experia box V10A from KPN
- FortiGate 60F (FortiOS 6.4)
- Internal switch where I can do some vlan-stuff with
You MUST use FortiOS 6.4 for this to work. Otherwise, the DHCP-client option which is used for iTV cannot be configured as this option is only available in FortiOS 6.4.
Update 5 dec 2022: some parts of this post are updated for FortiOS 7.2.
What did I want to realize?
I do not want to use the Experia box of KPN! I want to use my own FortiGate firewall to take over all the functions of the Experia box (apart from WiFi, where I have my own access-points)
What are the topics?
The topics to build are:
- Internet-connectivity (IPv4 & IPv6)
- iTV including replay and recordings
Building Internet
My ISP-connection is delivered over fiber, which is delivered with an UTP-connection from the NTU. The UTP cable is going directly into the WAN-port of my FortiGate.
Good to know is that KPN is providing me 3 vlans in total to carry their services:
- vlan 4 = iTV
- vlan 5 = Telephony
- vlan 6 = Internet
So, first I need to create a vlan-interface for vlan 6 on the WAN-port. Because of the PPPoE overhead, the MTU of the WAN-port needs to be set to 1514 bytes, and the vlan-interface itself needs to be set to 1506 bytes.
config system interface
edit "wan1"
set mtu-override enable
set mtu 1514
next
edit "internet"
set alias "vlan6"
set estimated-upstream-bandwidth 200000
set estimated-downstream-bandwidth 200000
set role wan
set snmp-index 8
set mtu-override enable
set mtu 1506
set interface "wan1"
set vlanid 6
next
endNext, we want to create the PPPoE-Interface. We bind this PPPoE-interface to the wan1 interface.
## This config is applicable to FortiOS 6.4 ##
config system interface
edit "pppoe1"
set mode pppoe
set allowaccess ping
set type tunnel
set estimated-upstream-bandwidth 200000
set estimated-downstream-bandwidth 200000
config ipv6
set ip6-mode dhcp
set ip6-allowaccess ping
set dhcp6-prefix-delegation enable
end
set interface "internet"
next
end## This part is for FortiOS 7.2. The v6-ranges should match the range which is received from KPN ##
config system interface
edit "wan1"
set vdom "root"
set status down
set type physical
set alias "KPN"
set role wan
set mtu-override enable
set mtu 1506
next
edit "pppoe"
set vdom "root"
set mode pppoe
set allowaccess ping
set type tunnel
set alias "internet"
set role wan
config ipv6
set ip6-mode dhcp
set dhcp6-prefix-delegation enable
config dhcp6-iapd-list
edit 5
set prefix-hint 2a02:aaaa:bbbb::/48
next
end
end
set interface "wan1"
next
endNote the config ipv6 IPv6 part; this part is neccesary to get an IPv6-prefix, which is advertised by the ISP via DHCPv6 prefix-delegation or DHCPv6-PD.
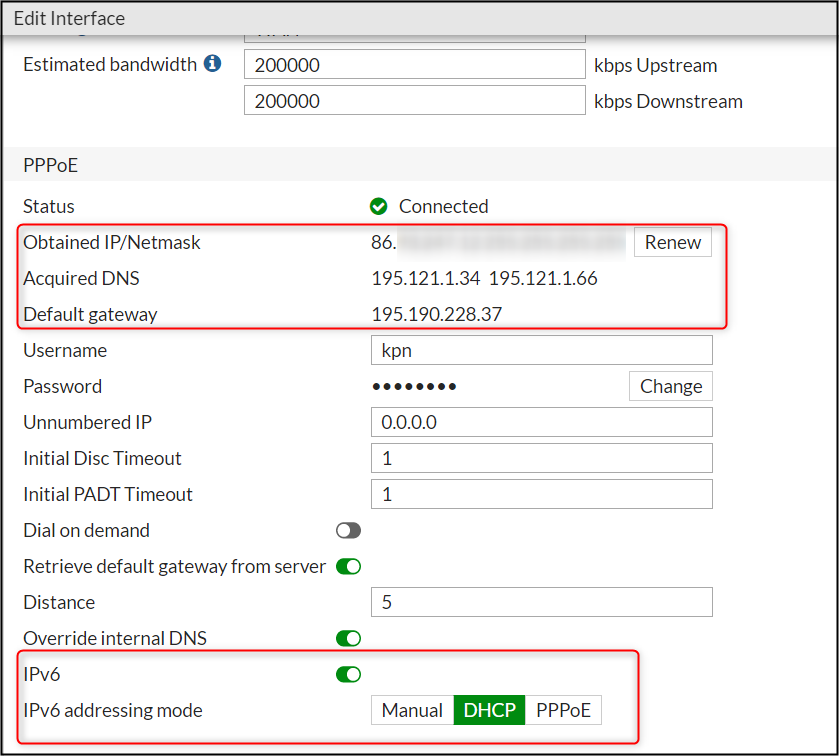
When we take a look of the PPPoE interface-part in the GUI of the FortiGate, you should see the IPv4 address which we have got from KPN.
we can also see that there is nothing visible about the DHCPv6-PD config. So, this part is only visible (and configurable) under the CLI.
If everything is okay, it should be possible to send some pings to hosts on the Internet over IPv4.
FGT60F # execute ping www.google.com
PING www.google.com (172.217.19.196): 56 data bytes
64 bytes from 172.217.19.196: icmp_seq=0 ttl=119 time=3.4 ms
64 bytes from 172.217.19.196: icmp_seq=1 ttl=119 time=3.4 ms
64 bytes from 172.217.19.196: icmp_seq=2 ttl=119 time=3.4 ms
64 bytes from 172.217.19.196: icmp_seq=3 ttl=119 time=3.4 ms
64 bytes from 172.217.19.196: icmp_seq=4 ttl=119 time=3.4 ms
--- www.google.com ping statistics ---
5 packets transmitted, 5 packets received, 0% packet loss
round-trip min/avg/max = 3.4/3.4/3.4 msIf your ping is working, then you have succesfully configured an IPv4 Internet-connection with your FortiGate. Now you can start with building your IPv4 policy-rules for your internal vlan (which is not part of this post).
At this moment, it is not possible (yet) to ping an IPv6 host on the Internet:
FGT60F # execute ping6 ipv6.google.com
connect: Network is unreachableThe ping6 is not working because there is no route for IPv6 defined. We need to do this statically. We point the IPv6 default-route to the pppoe1 interface.
config router static6
edit 1
set device "pppoe1"
next
endAfter this, you should be able to ping an IPv6 host:
FGT60F # exec ping6 ipv6.google.com
PING ipv6.google.com(2a00:1450:400e:806::200e) 56 data bytes
64 bytes from 2a00:1450:400e:806::200e: icmp_seq=1 ttl=120 time=3.71 ms
64 bytes from 2a00:1450:400e:806::200e: icmp_seq=2 ttl=120 time=3.73 ms
64 bytes from 2a00:1450:400e:806::200e: icmp_seq=3 ttl=120 time=3.66 ms
64 bytes from 2a00:1450:400e:806::200e: icmp_seq=4 ttl=120 time=3.66 ms
64 bytes from 2a00:1450:400e:806::200e: icmp_seq=5 ttl=120 time=3.68 msNow IPv6 is working to the outside world, we need to route it internally so that hosts can get an IPv6 address (Global Unicast). Therefore, we need to configure an IPv6-prefix on the inside interface of the FortiGate.
As KPN is giving you a /48 prefix, we can assign an /64 prefix to the internal network. The hosts which are internally, are getting an IPv6 address using SLAAC, which is the most easiest way to address your hosts for IPv6. Another option is to configure DHCPv6 (not part of this post).
Note that the 2a02:xxxx:xxxx:xxxx::/64 part of the config should be your IPv6 range which is allocated to you by KPN. If you don’t know this prefix, you can find this when you connect your Experia box and take a look in the web-interface.
## This part is applicable to FortiOS 6.4 ##
config system interface
edit "internal"
set ip 10.1.1.1 255.255.255.0
set allowaccess ping https ssh http fgfm
set role lan
config ipv6
set ip6-mode delegated
set ip6-allowaccess ping
set ip6-send-adv enable
set ip6-upstream-interface "pppoe1"
set ip6-subnet 2a02:xxxx:xxxx:xxxx::/64
config ip6-delegated-prefix-list
edit 1
set upstream-interface "pppoe1"
set subnet 2a02:xxxx:xxxx:xxxx::/64
next
end
end
next
end## This part is applicable to FortiOS 7.2. Mention the "5" for the prefix-iaid. This number MUST MATCH the dhcp6-iapd-list rule-index number (edit 5), which is under the pppoe logical-interface ##
edit "internal"
set vdom "root"
set ip 10.1.1.1 255.255.255.0
set allowaccess ping https ssh fabric
set type hard-switch
set role lan
config ipv6
set ip6-send-adv enable
config ip6-delegated-prefix-list
edit 1
set upstream-interface "pppoe"
set delegated-prefix-iaid 5
set subnet 2a02:aaaa:bbbb:10::/64
next
end
end
next
endWhen this config is done, you should be able to check if the IPv6-prefix is allocated to the internal interface.
FGT60F # diagnose ipv6 address list
#--- output ommitted ---
dev=25 devname=internal flag= scope=0 prefix=64 addr=2a02:xxxx:xxxx:xxxx:: preferred=171972 valid=258372 cstamp=10939 tstamp=10939
#--- output ommitted ---Note: I’ve seen that I need to restart the firewall to get this step done.
The final thing to do to get IPv6 working for your hosts, is to create a policy-rule for v6 in the FortiGate without NAT. Since NAT is not usual with IPv6, we do not enable this.
config firewall policy
edit 0
set name "outbound-internet v6"
set srcintf "internal"
set dstintf "pppoe1"
set srcaddr6 "all"
set dstaddr6 "all"
set action accept
set schedule "always"
set service "ALL"
set utm-status enable
next
endNow, as we take an internal host (I have a Win10 PC) then you can try to do an ipconfig /all to see your IPv6 addresses (you will get 2 temporary adresses).

Test your IPv6 connectivity: https://ipv6-test.com/
Building interactive-TV
See part 2.
Hi Peter, you made it look so simple that it made me test it out for myself. And yes, it works as simple as you wrote. But if i want to add additional /64 prefixes on different interfaces, it does not work. Have you tried that already? On the “internal” interface i get an IP address within the defined subnet but on the “guest” interface, it does not. Below the snippets from the interfaces
Internal:
config ipv6
set ip6-mode delegated
set ip6-allowaccess ping
set dhcp6-prefix-delegation enable
set ip6-send-adv enable
set ip6-manage-flag enable
set ip6-other-flag enable
set ip6-link-mtu 1472
set ip6-upstream-interface “WAN-VLAN6-PPPOE”
set ip6-subnet ::1:0:0:0:1/64
config ip6-delegated-prefix-list
edit 1
set upstream-interface “WAN-VLAN6-PPPOE”
set subnet 0:0:0:1::/64
next
end
end
Guest:
config ipv6
set ip6-mode delegated
set ip6-allowaccess ping
set dhcp6-prefix-delegation enable
set ip6-send-adv enable
set ip6-manage-flag enable
set ip6-other-flag enable
set ip6-link-mtu 1472
set ip6-upstream-interface “WAN-VLAN6-PPPOE”
set ip6-subnet ::3:0:0:0:1/64
config ip6-delegated-prefix-list
edit 1
set upstream-interface “WAN-VLAN6-PPPOE”
set subnet 0:0:0:3::/64
next
end
end
Any ideas?
And i’m really waiting on the I-TV setup of yours. I got i working for live TV but “uitzending gemist” and pause do not work yet. And got a ticket with fortinet support for the option 121. As i’m struggling to find the correct code and value.
Jeroen
Hi Jeroen. Thank you for your comment. I will publish the iTV part soon. And I will do some testing with the additional /64’s on additional interfaces.
Hi Jeroen, I have tested to configure ipv6 prefixes on multiple internal interfaces. This works as expected. I have the following config-snip on an internal interface. In this example, I only change the “99” part for the different interfaces, which equals the internal vlan-ID in my network.
config ipv6
set ip6-mode delegated
set ip6-allowaccess ping
set ip6-send-adv enable
set ip6-upstream-interface “pppoe-kpn”
set ip6-subnet 2a02:a453:abcd:99::/64
config ip6-delegated-prefix-list
edit 1
set upstream-interface “pppoe-kpn”
set subnet 2a02:a453:abcd:99::/64
next
end
hii
when i create the “pppoe1” interface i dont have the option “tunnel” for “set type ”
only
vlan
loopback
wl-mesh
emac-vlan
fortigate 60D v6.0.9
Hey Emre,
I have the same issue with the “set type tunnel” command. Have you found an solution to the problem?
Further I had some problems with the “interface” but fixed that with adding “set vdom root”
Fortigate 60E V7.05 (I also tried V6.4, V7.2, V7.0)
Its a bit silly but when you use the GUI it works just fine.
If you check the GUI made pppoe connection in CLI you will see that it has added the “set type tunnel”.
Fortigate 60E V7.05
i also get an error for set interface “internet” entry not found
when i do get sys interface it shows up in the list as “internet”
i am sorry i am still learning
Peter,
Is this also possible with the FortiGate 60D.
Best regards,
Jan-Willem Woermeijer
To create the pppoe1 interface you need first need to add the following config:
config system pppoe-interface
edit “pppoe1”
set device “internet”
next
end
But stil I can’t get IPv6 working. Can anyone post the full interface configuration?
Great webpage! i still did not get the IPv6 working on Fortigate with KPN Fiber (private-GPON). This my config:
edit lan
config ipv6
set ip6-mode delegated
set ip6-allowaccess ping
set ip6-send-adv enable
set ip6-other-flag enable
set ip6-upstream-interface “internet”
set ip6-delegated-prefix-iaid 1
set ip6-subnet ::3:0:0:0:1/64
config ip6-delegated-prefix-list
edit 1
set upstream-interface “internet”
set subnet ::/64
set rdnss-service default
next
end
end
edit “wan”
set vdom “root”
set allowaccess ping
set type physical
set monitor-bandwidth enable
set role wan
set snmp-index 1
set dns-server-override disable
set mtu-override enable
set mtu 1514
next
edit “internet”
set vdom “root”
set mode pppoe
set allowaccess ping
set alias “vlan6”
set estimated-upstream-bandwidth 1024000
set estimated-downstream-bandwidth 1024000
set role wan
set snmp-index 14
config ipv6
set ip6-mode pppoe
set ip6-allowaccess ping
set dhcp6-prefix-delegation enable
config dhcp6-iapd-list
edit 1
set prefix-hint ::/48
next
end
end
set username “XX-XX-XX-XX-XX-XX@internet”
set password ENC xxxx
set dns-server-override disable
set mtu-override enable
set mtu 1506
set interface “wan”
set vlanid 6
next
end
Internet is working just fine, but i dont get any prefix on the internet via DHCPv6 from KPN. On the Experiabox i do get a prefix hint just fine. I also tried it with set ip6-mode dhcp, but not difference.
Tried with and without prefix-hint, not difference.
Any idea whats wrong here?
Thanks a lot
Hi Martin. Below you find the interface-configuration (wan1, pppoe, internal) which has worked for me. It is running now on FortiOS 7.2. Internally, IPv6 addresses are given to clients through SLAAC. The v6 address-range which is mentioned in the configuration is intended as a example; of course it should match your own v6 address-range.
config system interface
edit “wan1”
set vdom “root”
set status down
set type physical
set alias “KPN”
set role wan
set snmp-index 1
set mtu-override enable
set mtu 1506
next
edit “pppoe”
set vdom “root”
set mode pppoe
set allowaccess ping
set type tunnel
set alias “internet”
set role lan
set snmp-index 16
config ipv6
set ip6-mode dhcp
set dhcp6-prefix-delegation enable
config dhcp6-iapd-list
edit 5
set prefix-hint 2a02:aaaa:bbbb::/48
next
end
end
set interface “wan1”
next
edit “internal”
set vdom “root”
set ip 10.1.1.1 255.255.255.0
set allowaccess ping https ssh fabric
set type hard-switch
set role lan
set snmp-index 15
config ipv6
set ip6-send-adv enable
config ip6-delegated-prefix-list
edit 1
set upstream-interface “pppoe”
set delegated-prefix-iaid 5
set subnet 2a02:aaaa:bbbb:10::/64
next
end
end
next
You can check if you get an v6-address on the wan-side with the following command:
# diagnose ipv6 address list
HI Peter,
Klopt het dat jij je PPPoE sessie opbouwt over de WAN interface, gebruik je hiervoor geen VLAN tagging?
Met onderstaande config krijg ik geen DHCP adres op mijn WAN interface
config system interface
edit “wan2”
set vdom “root”
set type physical
set snmp-index 2
set mtu-override enable
set mtu 1514
next
edit “VLAN1001”
set vdom “root”
set ip 10.10.1.254 255.255.255.0
set allowaccess speed-test
set alias “Server VLAN”
set device-identification enable
set monitor-bandwidth enable
set role lan
config ipv6
set ip6-address 2a02:aaaa:bbbb:1001::1/64
set ip6-send-adv enable
set ip6-manage-flag enable
set ip6-other-flag enable
config ip6-prefix-list
edit 2a02:aaaa:bbbb:1001::/64
next
end
end
set interface “VLAN1”
set vlanid 1001
next
edit “VLAN2001”
set vdom “root”
set ip 10.20.1.254 255.255.255.0
set allowaccess speed-test
set alias “Intern VLAN”
set device-identification enable
set monitor-bandwidth enable
set role lan
config ipv6
set ip6-address 2a02:aaaa:bbbb:2001::1/64
set ip6-send-adv enable
set ip6-manage-flag enable
set ip6-other-flag enable
config ip6-prefix-list
edit 2a02:aaaa:bbbb:2001::/64
next
end
end
set interface “VLAN1”
set vlanid 2001
next
edit “KPN-INET-VL6”
set vdom “root”
set device-identification enable
set estimated-upstream-bandwidth 200000
set estimated-downstream-bandwidth 200000
set role wan
set interface “wan2”
set mtu-override enable
set mtu 1506
set vlanid 6
next
edit “KPN-PPPoE”
set vdom “root”
set mode pppoe
set type tunnel
set role wan
config ipv6
set ip6-mode dhcp
set dhcp6-prefix-delegation enable
config dhcp6-iapd-list
edit 5
set prefix-hint 2a02:aaaa:bbbb::/48
next
end
end
set dns-server-override disable
set interface “KPN-INET-VL6”
next
end
great article, however with new fortios I am unable to replicate.
do you have update for 7.4?
hi, anyone got this working in 7.4? set type tunnel not possible anymore, did some testing with conf sys pppoe but with no succes. any ideas? suggestions are welcome, regards, Martin
hi, anyone got ipv6 working in 7.4? set type tunnel not possible anymore, did some testing with conf sys pppoe but with no succes. any ideas? suggestions are welcome, regards, Martin
Hi, I got it working in 7.4.7 with multiple vlans and will share below:
Note:
1 – This config is static IPv6, but if you add a IPv6 DHCP server on your LAN interfaces in GUI after config below, it should work aswell!
2 – Don’t forget to edit the PPPoE tunnel interface in GUI en add username and password. “KPN”
for IPv4 only.
3 – IPv6 on the PPPoE tunnel is set on DHCP and say “Connecting…”, this is OK.
4 – Change the 2A02:XXXX:YYYY::/48 with your own subnet, you can retrieve it in the My KPN app on your smartphone.
Config:
###########
#External:#
###########
config system interface
edit “wan1”
set vdom “root”
set type physical
set alias “Uplink_Fiber”
set role wan
set mtu-override enable
set mtu 1512
next
edit “VLAN6”
set vdom “root”
set alias “KPN-Internet-VLAN”
set role wan
set interface “wan1”
set mtu-override enable
set mtu 1508
set vlanid 6
next
edit “pppoe0”
set vdom “root”
set mode pppoe
set allowaccess ping
set type tunnel
set alias “Internet”
set role wan
config ipv6
set ip6-mode dhcp
set dhcp6-prefix-delegation enable
config dhcp6-iapd-list
edit 1
set prefix-hint 2A02:XXXX:YYYY::/48
next
end
end
set interface “VLAN6”
next
end
###########
#Internal:#
###########
edit “internal”
set vdom “root”
set ip 192.168.1.254 255.255.255.0
set allowaccess ping https ssh http
set type hard-switch
set description “Uplink_Managed_Switch_TRUNK”
set alias “LAN”
set role lan
config ipv6
set ip6-mode delegated
set ip6-allowaccess ping
set ip6-send-adv enable
set ip6-manage-flag enable
set ip6-other-flag enable
set ip6-delegated-prefix-iaid 1
set ip6-upstream-interface “pppoe0”
set ip6-subnet 2A02:XXXX:YYYY:1::254/64
config ip6-delegated-prefix-list
edit 1
set upstream-interface “pppoe0”
set subnet 2A02:XXXX:YYYY:1::/64
set rdnss-service default
next
end
end
next
edit “VLAN30”
set vdom “root”
set ip 192.168.30.254 255.255.255.0
set allowaccess ping
set alias “CCTV-CAM”
set role lan
config ipv6
set ip6-mode delegated
set ip6-allowaccess ping
set ip6-send-adv enable
set ip6-manage-flag enable
set ip6-other-flag enable
set ip6-delegated-prefix-iaid 1
set ip6-upstream-interface “pppoe0”
set ip6-subnet 2A02:XXXX:YYYY:30::254/64
config ip6-delegated-prefix-list
edit 1
set upstream-interface “pppoe0”
set subnet 2A02:XXXX:YYYY:30::/64
set rdnss-service default
next
end
end
set interface “internal”
set vlanid 30
next
edit “VLAN50”
set vdom “root”
set ip 192.168.50.254 255.255.255.0
set allowaccess ping
set alias “IOT-Smarthome”
set role lan
config ipv6
set ip6-mode delegated
set ip6-allowaccess ping
set ip6-send-adv enable
set ip6-manage-flag enable
set ip6-other-flag enable
set ip6-delegated-prefix-iaid 1
set ip6-upstream-interface “pppoe0”
set ip6-subnet 2A02:XXXX:YYYY:50::254/64
config ip6-delegated-prefix-list
edit 1
set upstream-interface “pppoe0”
set subnet 2A02:XXXX:YYYY:50::/64
set rdnss-service default
next
end
end
set interface “internal”
set vlanid 50
next
edit “VLAN90”
set vdom “root”
set ip 192.168.90.254 255.255.255.0
set allowaccess ping
set alias “Guest-Gasten”
set role lan
config ipv6
set ip6-mode delegated
set ip6-allowaccess ping
set ip6-send-adv enable
set ip6-manage-flag enable
set ip6-other-flag enable
set ip6-delegated-prefix-iaid 1
set ip6-upstream-interface “pppoe0”
set ip6-subnet 2A02:XXXX:YYYY:90::254/64
config ip6-delegated-prefix-list
edit 1
set upstream-interface “pppoe0”
set subnet 2A02:XXXX:YYYY:90::/64
set rdnss-service default
next
end
end
set interface “internal”
set vlanid 90
next
end
#####################
#IPv6 Default route:#
#####################
config router static6
edit 1
set device “pppoe0”
next
end